Recently Microsoft announced that a new Azure Firewall service was entering a managed public preview. Azure Firewall is a managed, network security service that protects your Azure Virtual Network resources. It is a fully stateful firewall as a service with built-in high availability and scalability.

The services uses a static public IP meaning that your outbound traffic can be identified by third party services as/if required. Worth nothing, that only outbound rules are active within this preview. Inbound filtering will hopefully be available by GA.
The following capabilities are all available as part of the preview:
- Stateful firewall as a Service
- Built-in high availability with unrestricted cloud scalability
- FQDN filtering
- Network traffic filtering rules
- Outbound SNAT support
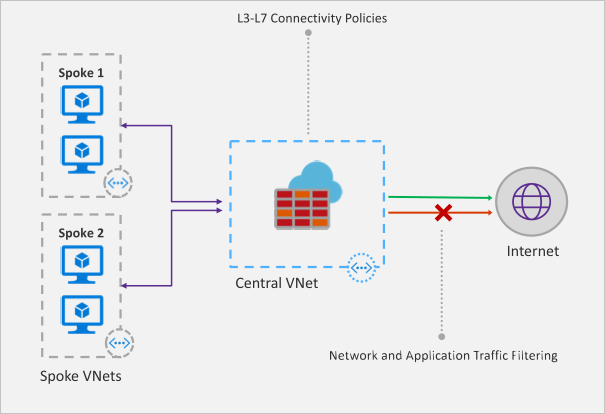
- Centrally create, enforce, and log application and network connectivity policies across Azure subscriptions and VNETs
- Fully integrated with Azure Monitor for logging and analytics
As with all previews it should not be used for production environments, but for testing purposes this is how to register your tenant for deployment.
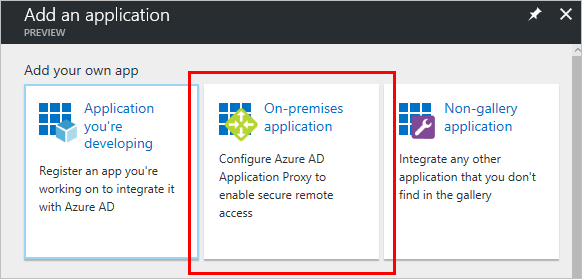
To enable the Azure Firewall public preview follow the guide here: Enabling the preview
Once enabled, follow this tutorial for a sample implementation: Deployment Tutorial
Now that you’re familiar with the deployment, you should apply to your specific test scenarios. Be wary of some operations that could be limited by applying a default route to your VM. There is an updated FAQ for the service here: Azure Firewall FAQ
Overall, this is a welcome addition to Azure networking. As the preview progresses and more service options are added, especially inbound options, I see this being as common as deploying an NSG in your environment. Combining it with peering and the right set of rule collections for your environment allows for an easily managed, scalable, and most importantly, secure environment within Azure with minimal cost and infrastructure footprint.